As an automation expert, you are likely familiar with the benefits of using Ansible as a configuration management tool. Ansible is a powerful automation platform that allows you to manage your infrastructure and automate repetitive tasks. However, one critical concern when using Ansible is the protection of sensitive information such as passwords, access keys, and other confidential data. Fortunately, Ansible provides a way to protect this information using the no_log statement.
The no_log statement is a powerful feature in Ansible that allows you to prevent sensitive data from being logged or stored in your logs. This statement is particularly useful when working with playbooks that involve sensitive data such as passwords or access keys. By default, Ansible logs all output to the console and to a log file. However, when the no_log statement is added to a task, Ansible will not log any output from that task to the console or log file.
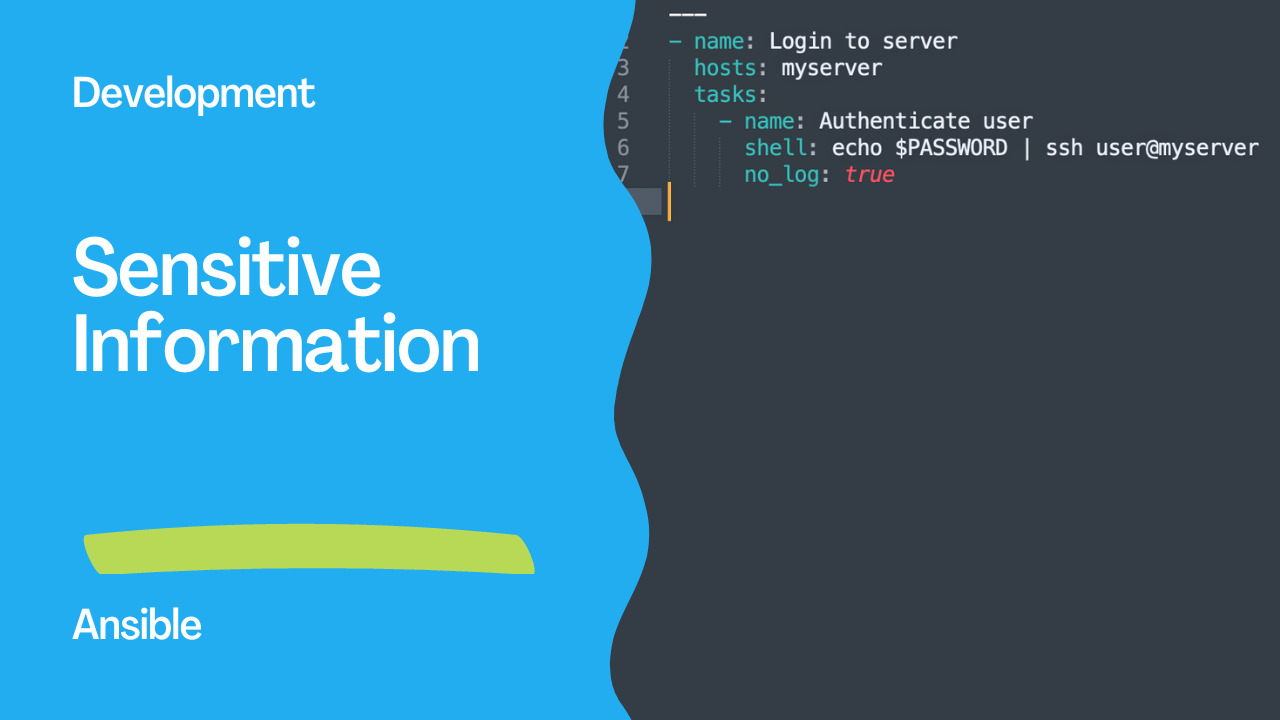
To use the no_log statement, you simply need to add it to the task where sensitive information is used. For example, if you are using a task that involves logging into a server using a password, you can add the no_log statement to the task to prevent the password from being logged. Here’s an example:
- name: Login to server
hosts: myserver
tasks:
- name: Authenticate user
shell: echo $PASSWORD | ssh user@myserver
no_log: true
In this example, the no_log statement has been added to the task that involves logging into the server. This ensures that the password is not logged or stored in any logs. It’s essential to note that the no_log statement only applies to the task where it is used. If the same sensitive data is used in another task, the no_log statement must be added to that task as well.
In addition to the no_log statement, Ansible also provides other methods to protect sensitive data, such as using Ansible Vault. Ansible Vault is a feature that allows you to encrypt sensitive data using a password. The encrypted data can then be stored in your playbooks or inventory files, and Ansible will automatically decrypt the data when it’s needed.

Links
Conclusion
In conclusion, protecting sensitive information is critical when working with Ansible. Using the no_log statement is one way to prevent sensitive data from being logged or stored in logs. By adding the no_log statement to tasks where sensitive data is used, you can ensure that your logs don’t contain any confidential information. Additionally, Ansible Vault is another powerful tool that you can use to encrypt sensitive data. By combining these methods, you can be confident that your sensitive information is protected when using Ansible.
Subscribe to the YouTube channel, Medium, and Website, X (formerly Twitter) to not miss the next episode of the Ansible Pilot.
Academy
Learn the Ansible automation technology with some real-life examples in my
Udemy 300+ Lessons Video Course.
My book Ansible By Examples: 200+ Automation Examples For Linux and AWX System Administrator and DevOps
Donate
Want to keep this project going? Please donate