Introduction
Ansible is a powerful automation tool that simplifies configuration management, application deployment, and task automation. Ensuring the quality and consistency of Ansible content is crucial for effective automation. Ansible-lint is a popular linting tool that helps identify issues and enforce best practices in Ansible playbooks, roles, and collections. Ansible-lint introduces the concept of profiles to gradually increase rule strictness throughout the content lifecycle.
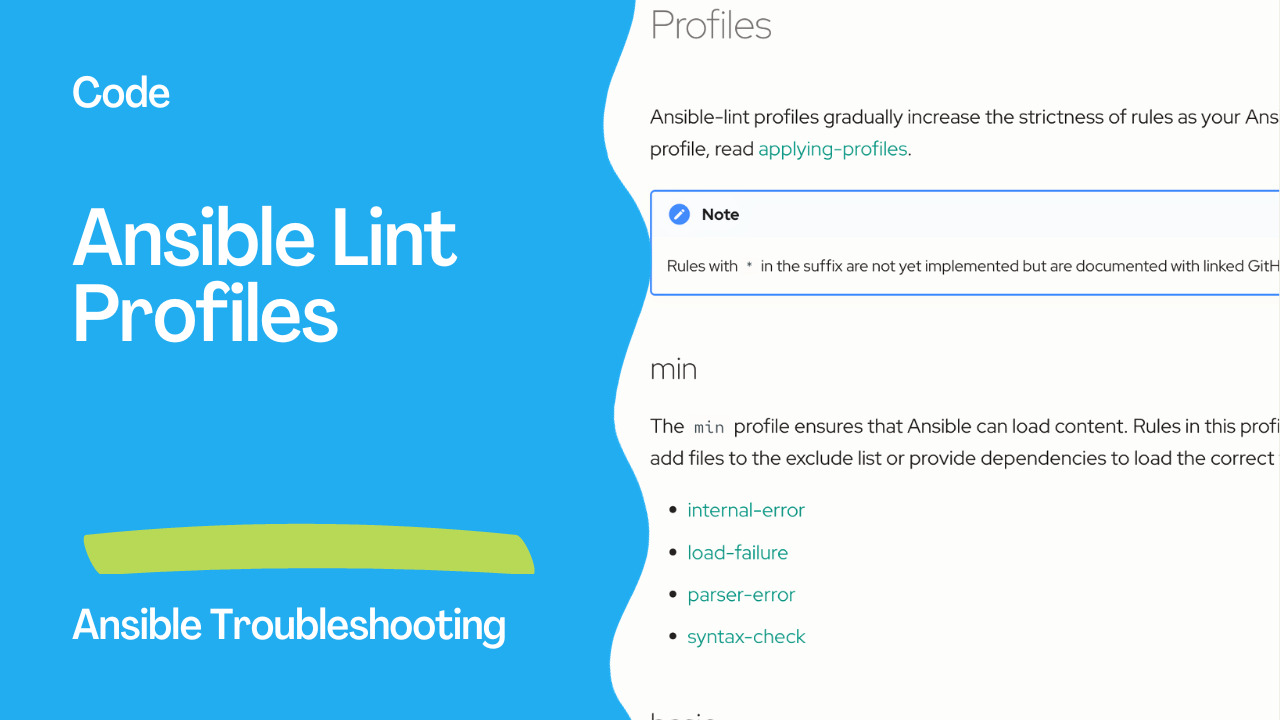
Understanding Ansible-Lint Profiles
Ansible-lint profiles provide a structured way to manage linting rules based on the desired level of strictness. As your Ansible content evolves, you can apply different profiles to catch potential issues early in development and ensure compliance with best practices. Let’s explore the available profiles and their purposes:
1. Min Profile
The min profile serves as the foundation, ensuring Ansible can load content without fatal errors. Rules in this profile are mandatory and include:
internal-error: Prevent internal errors.load-failure: Ensure content can be loaded.parser-error: Identify parsing errors.syntax-check: Verify syntax correctness.
Developers can customize the profile by excluding specific files or providing dependencies to load the correct files.
2. Basic Profile
Building upon the min profile, the basic profile addresses common coding issues and enforces standard styles and formatting. Key rules in this profile include:
command-instead-of-module: Detect the use of command instead of module.deprecated-bare-vars: Identify deprecated bare variables.key-order: Enforce key order.no-tabs: Prevent the use of tabs.
3. Moderate Profile
The moderate profile focuses on improving code readability and maintainability. It extends the basic profile with rules such as:
name[template]: Enforce template naming conventions.name[casing]: Ensure consistent naming conventions.jinja: Check for Jinja-related issues.
4. Safety Profile
The safety profile addresses non-determinant outcomes and security concerns. It extends the moderate profile with rules like:
avoid-implicit: Avoid implicit behaviors.risky-file-permissions: Identify risky file permissions.risky-shell-pipe: Detect risky shell pipe operations.
5. Shared Profile
The shared profile is designed for content creators who want to publish their Ansible content. It builds upon the safety profile and includes rules like:
galaxy: Ensure compliance with Galaxy best practices.layout: Enforce a standardized directory layout.meta-incorrect: Identify incorrect metadata.
6. Production Profile
The production profile sets the highest level of strictness, ensuring content meets the requirements for inclusion in Ansible Automation Platform (AAP). Rules include:
avoid-dot-notation: Discourage the use of dot notation.sanity: Ensure overall code sanity.single-entry-point: Enforce a single entry point.
Applying Ansible-Lint Profiles
To apply a specific profile, developers can refer to the documentation on applying profiles. The flexibility of Ansible-lint profiles empowers teams to tailor linting rules according to their specific needs and development workflows.
Applying Ansible-Lint profiles is a fundamental step in enhancing the quality of Ansible playbooks, roles, and collections throughout their development lifecycle. In the initial stages, adopting the minimal profile is crucial to ensuring the loading capability of Ansible content. As the development progresses, content creators can systematically apply profiles with increasing strictness to address common issues and enhance code readability. When preparing to share or publish the content, leveraging the shared and production profiles becomes imperative, imposing stringent rules to bolster security and reliability. These profiles not only contribute to the robustness of Ansible automation but also facilitate collaboration by ensuring that the content is easily understandable and accessible to others. It is worth noting that tags like opt-in and experimental don’t impact rules included in profiles, and Ansible-lint applies rules in profiles directly or indirectly. Applying profiles is straightforward; after installing and configuring ansible-lint, users can list available profiles and specify a desired profile using the --profile parameter, allowing for the seamless enforcement of linting rules tailored to the specific needs of each development stage.
Enforce standard styles and formatting with the basic profile.
ansible-lint --profile=basic
Ansible-lint profiles provide a systematic approach to linting Ansible content at different stages of development. By applying appropriate profiles, developers can catch issues early, maintain code quality, and ensure their Ansible automation is robust and compliant with best practices. We can configure the profile in a configuration file in our project.
.ansible-lint
profile: basic # min, basic, moderate,safety, shared, production
enable_list:
- args
- empty-string-compare # opt-in
- no-log-password # opt-in
- no-same-owner # opt-in
- name[prefix] # opt-in

Linting vs Syntax-Checking
It’s important to distinguish between linting and syntax-checking in Ansible. Syntax-checking ensures that your code adheres to YAML formatting rules and is free of basic syntax errors. You can perform syntax-checking using Ansible’s built-in tool with the following command:
ansible-playbook --syntax-check playbook.yml
Linting, as discussed in this article, goes a step further. It not only checks syntax but also enforces best practices, code consistency, and identifies potential issues that may not be apparent during syntax-checking.
Conclusion
In conclusion, Ansible-lint profiles provide a systematic approach to linting Ansible content at different stages of development. By applying appropriate profiles, developers can catch issues early, maintain code quality, and ensure their Ansible automation is robust and compliant with best practices.
Linting Ansible playbooks are crucial in maintaining code quality, consistency, and reliability in your infrastructure automation projects. ansible-lint provides a powerful set of rules and guidelines to help you catch errors, enforce best practices, and ensure your playbooks are written consistently and maintainably.
Academy
Learn the Ansible automation technology with some real-life examples in my
Udemy 300+ Lessons Video Course.
My book Ansible By Examples: 200+ Automation Examples For Linux and Windows System Administrator and DevOps
Donate
Want to keep this project going? Please donate