How to create Kubernetes K8s or OpenShift OCP secret with Ansible?
I’m going to show you a live Playbook and some simple Ansible code. I’m Luca Berton and welcome to today’s episode of Ansible Pilot.
Ansible create Kubernetes or OpenShift secret
kubernetes.core.k8s- Manage Kubernetes (K8s) objects
Let’s talk about the Ansible module k8s.
The full name is kubernetes.core.k8s, which means that is part of the collection of modules of Ansible to interact with Kubernetes and Red Hat OpenShift clusters.
It manages Kubernetes (K8s) objects.
Parameters
- name string /namespace string - object name / namespace
- api_version string - “v1”
- kind string - object model
- state string - present/absent/patched
- definition string - YAML definition
- src path - path for YAML definition
- template raw - YAML template definition
- validate dictionary - validate resource definition
There is a long list of parameters of the k8s module. Let me summarize the most used.
Most of the parameters are very generic and allow you to combine them for many use-cases.
The name and namespace specify object name and/or the object namespace. They are useful to create, delete, or discover an object without providing a full resource definition.
The api_version parameter specifies the Kubernetes API version, the default is “v1” for version 1.
The kind parameter specifies an object model.
The state like for other modules determines if an object should be created - present option, patched - patched option, or deleted - absent option.
The definition parameter allows you to provide a valid YAML definition (string, list, or dict) for an object when creating or updating.
If you prefer to specify a file for the YAML definition, the src parameter provides a path to a file containing a valid YAML definition of an object or objects to be created or updated.
You could also specify a YAML definition template with the template parameter.
You might find useful also the validate parameter in order to define how to validate the resource definition against the Kubernetes schema. Please note that requires the kubernetes-validate python module.
Links

Playbook
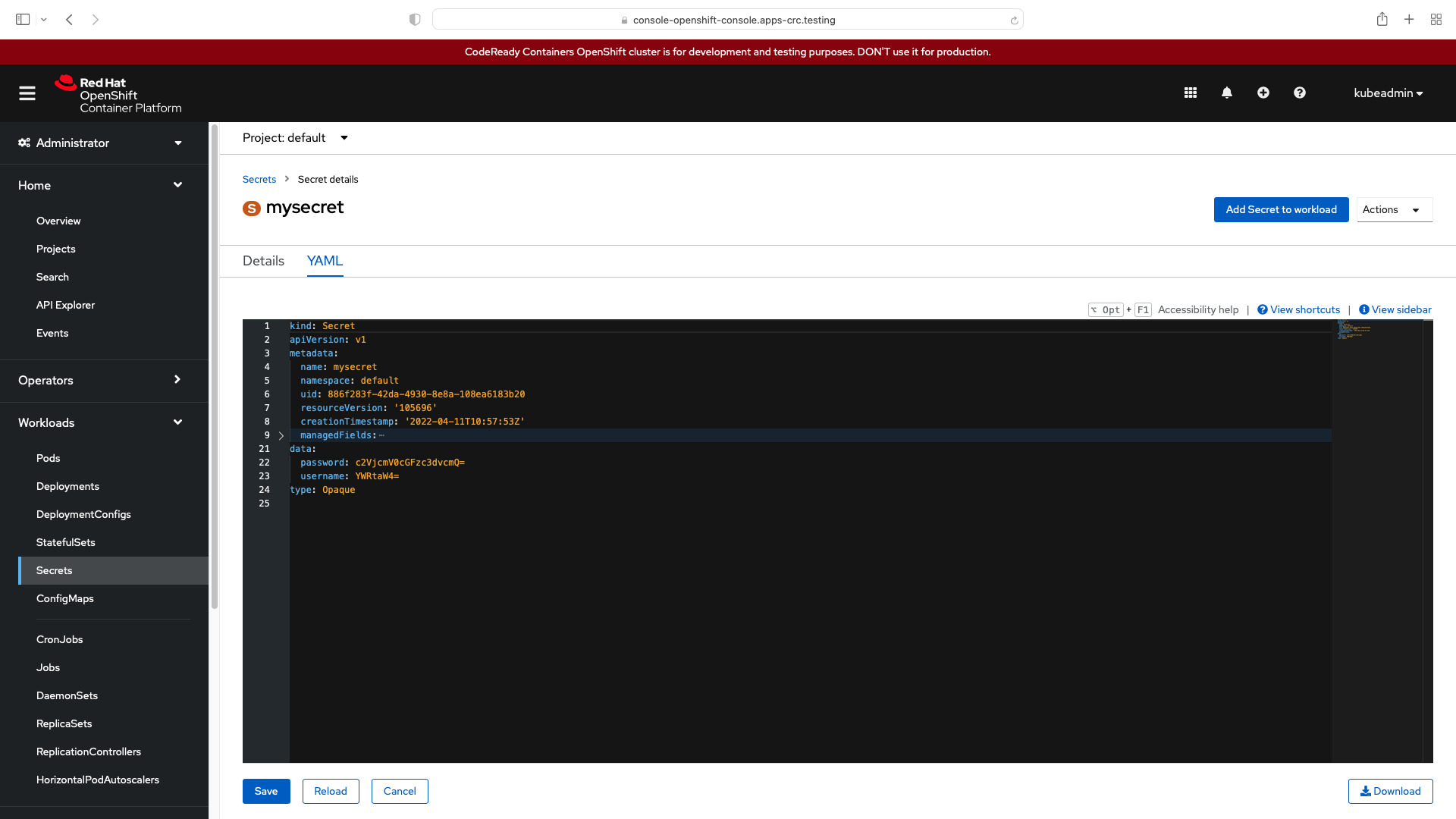
How to create Kubernetes secret with Ansible Playbook using the module k8s. Specifically, the following example is going to create the “mysecret” secret in namespace “default” in Kubernetes K8s or OpenShift OCP with Ansible.
code
- ansible_playbook.yml
---
- name: k8s Playbook
hosts: localhost
gather_facts: false
connection: local
tasks:
- name: create k8s secret mysecret
kubernetes.core.k8s:
src: mysecret.yaml
state: present
- mysecret.yml
The values for all keys in the data the field has to be base64-encoded strings. username = admin, password = secretpassword
---
apiVersion: v1
kind: Secret
metadata:
name: mysecret
namespace: default
type: Opaque
data:
username: YWRtaW4=
password: c2VjcmV0cGFzc3dvcmQ=
execution
ansible-pilot $ ansible-playbook kubernetes/secret.yml
[WARNING]: No inventory was parsed, only implicit localhost is available
[WARNING]: provided hosts list is empty, only localhost is available. Note that the implicit
localhost does not match 'all'
PLAY [k8s Playbook] ***********************************************************************************
TASK [create k8s secret mysecret] *****************************************************************
changed: [localhost]
PLAY RECAP ****************************************************************************************
localhost : ok=1 changed=1 unreachable=0 failed=0 skipped=0 rescued=0 ignored=0
ansible-pilot $
idempotency
ansible-pilot $ ansible-playbook kubernetes/secret.yml
[WARNING]: No inventory was parsed, only implicit localhost is available
[WARNING]: provided hosts list is empty, only localhost is available. Note that the implicit
localhost does not match 'all'
PLAY [k8s Playbook] ***********************************************************************************
TASK [create k8s secret mysecret] *****************************************************************
ok: [localhost]
PLAY RECAP ****************************************************************************************
localhost : ok=1 changed=0 unreachable=0 failed=0 skipped=0 rescued=0 ignored=0
ansible-pilot $
before execution
- Kubernetes (k8s)
ansible-pilot $ kubectl list secrets
NAME TYPE DATA AGE
builder-dockercfg-sqm7r kubernetes.io/dockercfg 1 74d
builder-token-9tg7z kubernetes.io/service-account-token 4 74d
builder-token-rvhcn kubernetes.io/service-account-token 4 74d
default-dockercfg-lgth4 kubernetes.io/dockercfg 1 74d
default-token-6g2dp kubernetes.io/service-account-token 4 74d
default-token-x5l9r kubernetes.io/service-account-token 4 74d
deployer-dockercfg-9c5n2 kubernetes.io/dockercfg 1 74d
deployer-token-htqht kubernetes.io/service-account-token 4 74d
deployer-token-q74gz kubernetes.io/service-account-token 4 74d
example Opaque 2 1m
- OpenShift (OCP)
ansible-pilot $ oc list secrets
NAME TYPE DATA AGE
builder-dockercfg-sqm7r kubernetes.io/dockercfg 1 74d
builder-token-9tg7z kubernetes.io/service-account-token 4 74d
builder-token-rvhcn kubernetes.io/service-account-token 4 74d
default-dockercfg-lgth4 kubernetes.io/dockercfg 1 74d
default-token-6g2dp kubernetes.io/service-account-token 4 74d
default-token-x5l9r kubernetes.io/service-account-token 4 74d
deployer-dockercfg-9c5n2 kubernetes.io/dockercfg 1 74d
deployer-token-htqht kubernetes.io/service-account-token 4 74d
deployer-token-q74gz kubernetes.io/service-account-token 4 74d
example Opaque 2 1m
after execution
- Kubernetes (k8s)
ansible-pilot $ kubectl list secrets
NAME TYPE DATA AGE
builder-dockercfg-sqm7r kubernetes.io/dockercfg 1 74d
builder-token-9tg7z kubernetes.io/service-account-token 4 74d
builder-token-rvhcn kubernetes.io/service-account-token 4 74d
default-dockercfg-lgth4 kubernetes.io/dockercfg 1 74d
default-token-6g2dp kubernetes.io/service-account-token 4 74d
default-token-x5l9r kubernetes.io/service-account-token 4 74d
deployer-dockercfg-9c5n2 kubernetes.io/dockercfg 1 74d
deployer-token-htqht kubernetes.io/service-account-token 4 74d
deployer-token-q74gz kubernetes.io/service-account-token 4 74d
example Opaque 2 10m
mysecret Opaque 2 1m
- OpenShift (OCP)
ansible-pilot $ oc list secrets
NAME TYPE DATA AGE
builder-dockercfg-sqm7r kubernetes.io/dockercfg 1 74d
builder-token-9tg7z kubernetes.io/service-account-token 4 74d
builder-token-rvhcn kubernetes.io/service-account-token 4 74d
default-dockercfg-lgth4 kubernetes.io/dockercfg 1 74d
default-token-6g2dp kubernetes.io/service-account-token 4 74d
default-token-x5l9r kubernetes.io/service-account-token 4 74d
deployer-dockercfg-9c5n2 kubernetes.io/dockercfg 1 74d
deployer-token-htqht kubernetes.io/service-account-token 4 74d
deployer-token-q74gz kubernetes.io/service-account-token 4 74d
example Opaque 2 10m
mysecret Opaque 2 1m
Conclusion
Now you know how to create Kubernetes or OpenShift secret with Ansible.
Subscribe to the YouTube channel, Medium, and Website, X (formerly Twitter) to not miss the next episode of the Ansible Pilot.Academy
Learn the Ansible automation technology with some real-life examples in my
Udemy 300+ Lessons Video Course.
My book Ansible By Examples: 200+ Automation Examples For Linux and Windows System Administrator and DevOps
Donate
Want to keep this project going? Please donate