Introduction
In Ansible, the args rule is a critical aspect of ensuring that your playbook’s task arguments align with the plugin’s documentation. It’s vital to maintain a proper structure and adhere to the required parameters for each module. Failure to do so can lead to unexpected behavior and issues in your automation workflow.
This rule primarily serves as a validator, confirming that your task arguments are not only present but also correctly defined. It checks if the option names are valid and if they have the correct values. Additionally, it examines conditions related to these options, such as mutually exclusive, required together, required one of, and more.
Here are some possible messages that this rule might generate:
args[module] - missing required arguments: ...args[module] - missing parameter(s) required by ...
Let’s delve into some examples to understand this rule better.
Problematic Code
---
- name: Fixture to validate module options failure scenarios
hosts: all
tasks:
- name: Clone content repository
ansible.builtin.git: # <- Required option `repo` is missing.
dest: /home/www
accept_hostkey: true
version: master
update: false
- name: Enable service httpd and ensure it is not masked
ansible.builtin.systemd: # <- Missing 'name' parameter required by 'enabled'.
enabled: true
masked: false
- name: Use quiet to avoid verbose output
ansible.builtin.assert:
test:
- my_param <= 100
- my_param >= 0
quiet: invalid # <- Value for option `quiet` is invalid.
Output
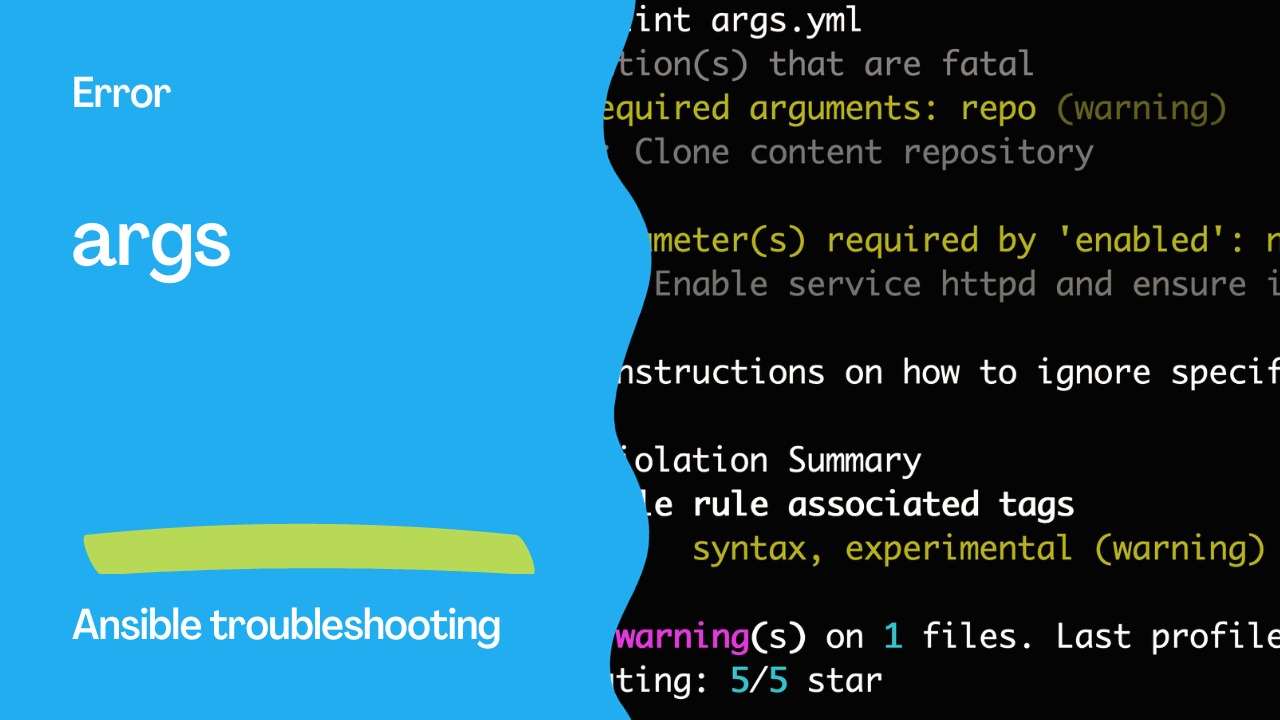
WARNING Listing 2 violation(s) that are fatal
args[module]: missing required arguments: repo (warning)
args.yml:5 Task/Handler: Clone content repository
args[module]: missing parameter(s) required by 'enabled': name (warning)
args.yml:12 Task/Handler: Enable service httpd and ensure it is not masked
Read documentation for instructions on how to ignore specific rule violations.
Rule Violation Summary
count tag profile rule associated tags
2 args[module] syntax, experimental (warning)
Passed: 0 failure(s), 2 warning(s) on 1 files. Last profile that met the validation criteria was 'production'. Rating: 5/5 star

Correct Code
---
- name: Fixture to validate module options pass scenario
hosts: all
tasks:
- name: Clone content repository
ansible.builtin.git: # <- Contains required option `repo`.
repo: https://github.com/ansible/ansible-examples
dest: /home/www
accept_hostkey: true
version: master
update: false
- name: Enable service httpd and ensure it is not masked
ansible.builtin.systemd: # <- Contains 'name' parameter required by 'enabled'.
name: httpd
enabled: false
masked: false
- name: Use quiet to avoid verbose output
ansible.builtin.assert:
that:
- my_param <= 100
- my_param >= 0
quiet: True # <- Has correct type value for option `quiet` which is boolean.
It’s essential to make sure that your task arguments align with the plugin documentation. Validating your module options using the args rule is a crucial step in maintaining a robust Ansible playbook and ensuring the success of your automation tasks.
In some special cases, such as when using Jinja expressions, the linter may not fully validate all possible values and could produce a false positive. In such scenarios, you can use # noqa: args[module] to bypass the rule for specific instances where validation is challenging.
Remember that proper task argument validation is key to achieving reliable and efficient automation with Ansible. The args rule is your ally in this endeavor, helping you catch and rectify issues before they impact your infrastructure automation.
Conclusion
In conclusion, the args rule in Ansible plays a pivotal role in ensuring the correctness and reliability of your automation playbooks. By validating task arguments against the documentation for Ansible modules, this rule helps maintain the integrity of your automation workflows.
By adhering to this rule, you can:
Ensure Correct Module Usage: The
argsrule verifies that you are using Ansible modules with the correct parameters and values as specified in the documentation. This reduces the risk of unintended behavior and errors in your tasks.Prevent Missing Parameters: The rule checks for missing parameters that are essential for the proper execution of a module. It alerts you to any omissions, helping you avoid incomplete or malfunctioning tasks.
Detect Invalid Values: It identifies cases where you provide incorrect or invalid values for module parameters, ensuring that your automation is based on valid configurations.
Adhere to Best Practices: Following this rule is a best practice that aligns your Ansible automation with the recommended standards. It promotes consistency and reliability across your playbooks.
However, in complex scenarios involving Jinja expressions or when the linter may not fully validate certain values, you have the flexibility to bypass the rule for specific instances using # noqa: args[module].
Overall, the args rule is a valuable tool for Ansible playbook development, helping you catch and rectify potential issues in your automation tasks before they impact your IT infrastructure. By making it an integral part of your Ansible development process, you can build robust, reliable, and efficient automation workflows that drive your organization’s success.
Academy
Learn the Ansible automation technology with some real-life examples in my
Udemy 300+ Lessons Video Course.
My book Ansible By Examples: 200+ Automation Examples For Linux and Windows System Administrator and DevOps
Donate
Want to keep this project going? Please donate