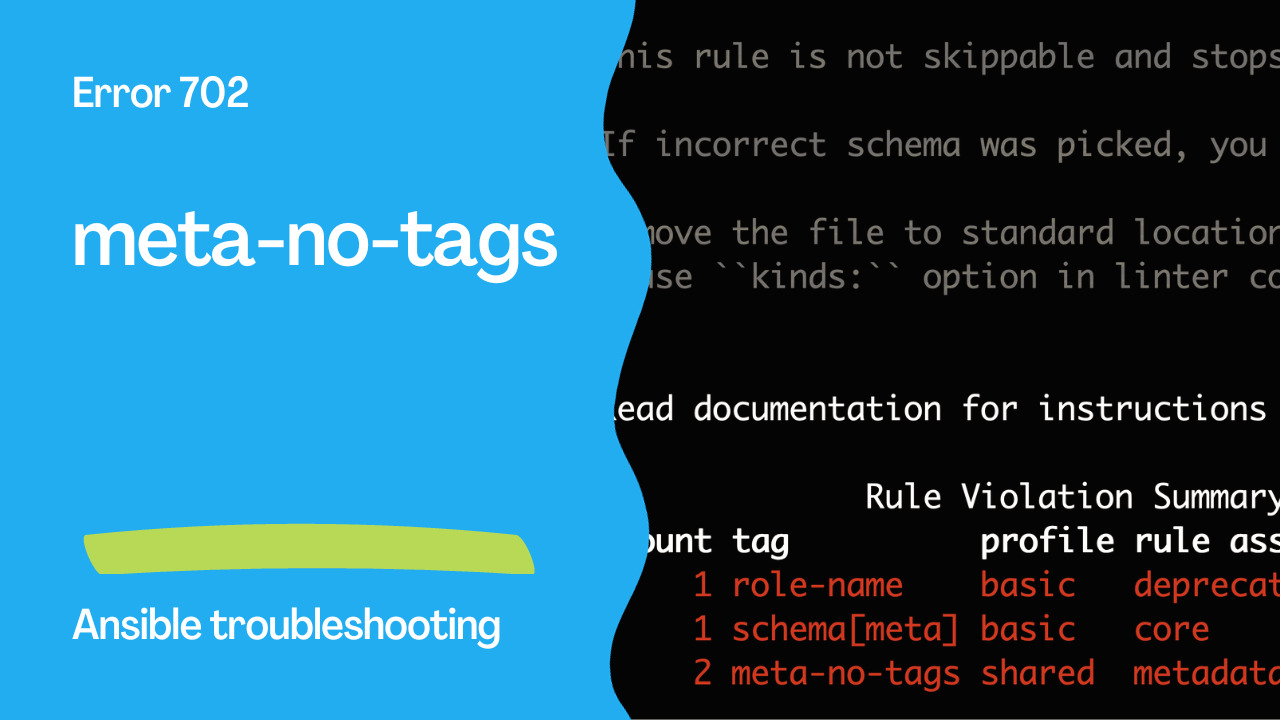
Introduction
Automation is a powerful ally for modern IT operations, and Ansible stands as one of the leading tools for managing complex tasks. When you’re working with Ansible, you often organize your automation logic into roles. Roles encapsulate a collection of tasks, templates, and variables that help automate specific functions within your infrastructure. However, even in the realm of automation, there are rules and conventions to follow to ensure your work is both efficient and understandable. Ansible Rule 702, “meta-no-tags,” focuses on a particular aspect of role management: metadata tags.
Understanding Metadata Tags
In Ansible, metadata tags are used to categorize and label roles and tasks. Tags help you filter and execute specific roles or tasks in your playbook. When it comes to organizing and naming these tags within the metadata of a role, Rule 702 comes into play.
The Significance of Rule 702
Rule 702, “meta-no-tags,” checks role metadata for tags with special characters and uppercase letters. It enforces the convention of using only lowercase letters and numbers for tags in the meta/main.yml file in an Ansible Role.
This might seem like a minor detail, but adhering to this rule is essential for maintaining consistent and organized Ansible roles.
Problematic Code vs. Correct Code
Let’s illustrate the difference between problematic code that violates Rule 702 and the correct code that aligns with the rule’s recommendations.
Problematic Code
Metadata tags contain uppercase letters and special characters.
meta/main.yml
---
galaxy_info:
author: Test
description: test
company: Test
license: GPL-2.0-or-later
min_ansible_version: 2.1
galaxy_tags: [MyTag#1, MyTag&^-]
dependencies: []
Output
WARNING Listing 4 violation(s) that are fatal
meta-no-tags: Tags must contain lowercase letters and digits only., invalid: 'MyTag#1'
702/meta/main.yml:1
meta-no-tags: Tags must contain lowercase letters and digits only., invalid: 'MyTag&^-'
702/meta/main.yml:1
role-name: Role name 702 does not match ``^[a-z][a-z0-9_]*$`` pattern.
702/meta/main.yml:1
schema[meta]: $.galaxy_info.min_ansible_version 2.1 is not of type 'string'. See https://docs.ansible.com/ansible/latest/playbook_guide/playbooks_reuse_roles.html#using-role-dependencies
702/meta/main.yml:1 Returned errors will not include exact line numbers, but they will mention
the schema name being used as a tag, like ``schema[playbook]``,
``schema[tasks]``.
This rule is not skippable and stops further processing of the file.
If incorrect schema was picked, you might want to either:
* move the file to standard location, so its file is detected correctly.
* use ``kinds:`` option in linter config to help it pick correct file type.
Read documentation for instructions on how to ignore specific rule violations.
Rule Violation Summary
count tag profile rule associated tags
1 role-name basic deprecations, metadata
1 schema[meta] basic core
2 meta-no-tags shared metadata
Failed: 4 failure(s), 0 warning(s) on 1 files. Last profile that met the validation criteria was 'min'.

Correct Code
---
# Metadata tags contain only lowercase letters and numbers.
galaxy_info:
galaxy_tags: [mytag1, mytag2]
As Playbooknstrated in the correct code, it’s important to stick to lowercase letters and numbers for your metadata tags. Avoid uppercase letters and special characters, as they can lead to inconsistencies and confusion when managing your roles and tasks.
Why Conform to Rule 702?
Adhering to Rule 702 brings several benefits to your Ansible role management:
1. Consistency: Using consistent naming conventions across roles and tasks makes it easier for you and your team to quickly identify and work with specific automation components.
2. Readability: Clean and well-organized metadata tags improve the readability of your roles and tasks, which is crucial for maintaining and troubleshooting your automation scripts.
3. Ease of Maintenance: When everyone follows the same conventions, it becomes much simpler to maintain and expand your roles over time.
Conclusion
In conclusion, Ansible Rule 702, “meta-no-tags,” ensures that your roles and tasks have consistent and readable metadata tags. By adhering to this rule, you enhance the manageability and maintainability of your Ansible automation, which is crucial for any successful IT operation. It’s a simple yet effective practice that can significantly impact the efficiency and reliability of your automation workflow.
Academy
Learn the Ansible automation technology with some real-life examples in my
Udemy 300+ Lessons Video Course.
My book Ansible By Examples: 200+ Automation Examples For Linux and Windows System Administrator and DevOps
Donate
Want to keep this project going? Please donate